Jordan Savant // Software Architect

- Links
- Pinned ❤
- 3D Graphics
- Anatomy of a Doom Level Part 1 WAD Structure
- Anatomy of a Doom Level Part 2 Creating a Doom Level
- Astar Pathfinding
- Binary Space Partitioning
- Bresenhams Line
- Cellular Automata
- Chaedinth Unicode Language
- CORS
- C++ Compiling And Linking
- CSRF
- JSON Web Tokens
- Making An Oblivion Mod Part 1
- Making An Oblivion Mod Part 2
- Neural Network Multilayer Perceptron
- Neural Network Perceptron
- OpenAI Project Spacebus
- Shadowcasting
- TOSty Chatbot
- TypeScript Example With Cellular Automota
- Algorithms
- Artificial Intelligence
- Data Storage
- Ascii Character Chart
- Elasticsearch
- Google Bigquery Cheatsheet
- MySQL
- Redis
- Editors
- Frameworks
- Game Dev
- Graphics
- Languages
- ADA
- Bash
- Bash 16 Colors
- Bash 256 Colors
- Bash Backup MySQL
- Bash Check Root User
- Bash Count Files
- Bash File Basename
- Bash For Loop
- Bash Function Output
- Bash Get Script Dir
- Bash Highlight Stream
- Bash Live
- Bash Merge Directories
- Bash Parallel Processing
- Bash Process Exists
- Bash Regex Match
- Bash Repeat Command Until Output
- Bash Rsync Backup
- Bash Store Command Output
- Bash String Length
- Bash String Replace
- Bash String Substring
- Bash Switch Statement
- Bash Tree
- Bash Until Loop
- C++
- Go
- JavaScript
- Node.js
- PHP
- Python
- TypeScript
- Math
- Modding
- Operating Systems
- Apache
- Docker
- FTP
- Linux
- Alias Syslog
- Apt Install Commands
- Bash Clear History
- Change User Group
- Clipboard From Command
- Color Output With Sed
- Colors
- Diff Strings
- Disc Usage
- Expand Fs
- File Information
- Find
- Fix Locale
- Full System Diagnostic
- Growl Bash
- Linux Kernel Dev Blog 1 Setup
- Linux Kernel Dev Blog 2 Code
- Linux Kernel Dev Blog 3 Email
- Linux Kernel Dev Blog 5 Linuxfromscratch
- Linux Kernel Dev Blog 6 Lfs Start
- Linux Kernel Dev Blog 7 Lfs Sources
- Linux Kernel Dev Blog 8 Lfs Compiling
- Linux Kernel Dev Blog 9 Lfs Compiling 2
- List Users
- Lprint
- Ls Dirs Only
- Mkdir
- Permissions
- Print System Info
- Reload Profile
- Rename Files
- Search For PHP Shorttags
- Sed Search Regex Replace
- SSH Environment Variable
- SSH Polling Command
- Sum File Lines
- Targz
- Time Process
- Ubuntu Increase Disk
- Unmount Remount
- Usage Message
- Whereis Command
- Zip
- OSX
- TMUX
- Windows
- Regular Expressions
- Security
- Version Control
- Git
- GIT Add Interactive
- GIT Alias
- GIT Apply Patch To File
- GIT Blame Historically
- GIT Branch See If Merged
- GIT Branch Switch Upstream
- GIT Check New Files For PHP Parse Errors
- GIT Checkout Interactive
- GIT Cherry Pick From Another Repo
- GIT Cherry Pick Interactive
- GIT Compress And Prune
- GIT Diff
- GIT Diff Show Deleted Files
- GIT Find Branch Commit Came From
- GIT Hooks
- GIT List All Tracked Files
- GIT Log Branch Commits
- GIT Log Commits From Specific Branch
- GIT Log Commits In Branch a Not In Branch B
- GIT Log Commits Local Only
- GIT Migrate Repo
- GIT Reflog Date
- GIT Remove Branch
- GIT Revert Without Commit
- GIT Show Aliases
- GIT Show Exclude Directories
- GIT Show Staged Changes Only
- GIT Stash Show
- GIT Stash Unstaged
- GIT Undo Commit Unpushed
- GIT Version
- Subversion
Welcome
I am Jordan Savant a software enginner and architect and this is my website. It mostly contains engineering write ups on algorithms, data structures and programming topics. Feel free to explore. Almost all code is written by myself, but some is for reference only so make sure before copying directly.
A little about myself: I am a 20+ year software engineer. I started developing when I was a kid with TI-Basic on Texas Instruments calculators. I fell in love and and have been programming software ever since.
I am currently employed as a Senior Software Architect at software development Lifeblue. I help lead a team of bright devs that keep me on my toes and continue to grow with our ever changing field. On the side I explore independent game development as a hobby, some available on Steam.
Below you will find a list of topics and projects I have found interesting. I have tried to keep performance, privacy and accessibility first in mind as you peruse the site.
Chaedinth Unicode Language
Read the new article about how to create custom languages by creating custom fonts for glyphs, overriding unicode positions and rendering out to the screen. Take a look at this inline sampling:
ÌåÉ ìÔ êÙÖ Øé Ñæ ÖØçÎÏ Øé ÖæÉ íÈëØ Ìë Ûî ÎãÔ ÐäÎ ÛéÖ ìÔ ÏäÔËÚçÍø Ûî Ðä Èæ äÈÏ Øé ÖæÉ Ñç× ÚíÔ× Ûî ÌãÙ ËçÙíÔ çØ ×íÐ åÊÖØù
With these techniques you will learn how to create icons, glyphs and symbols that can be rendered inline alongside any other unicode or alphabetical symbols all using the native rendering of the browser or game engine that has loaded your unique font.
Indie Game Development
View where my game development projects are showcased and released. It includes titles primarily published on Steam and iOS. Check out the Indie Games page.

Current Opinion on AI
As an engineer I use LLM-based AI on a weekly basis to distill down information that the old SEO giants of yester-year can no longer surface. I also utilize companion AI tools to enhance autocompletion of code reducing the amount of typing and menial problem solving. I have taken as stab at creating small-scale, single page, web-apps using AI tools like Claude and the results are impressive. However, extending and debugging these sample applications have proven challenging given its generation of useless blocks of code, it's opaque reasoning and unabstracted capabilities.
With the advent of AI in the form of large language models and video/audio generation many see this time period as the beginning of a major disruption of many industries including software engineering. Unfortunately the loudest voices heralding this message come from executives and business owners of AI based startups which have a vested interest in the narrative that their businesses are the future and all of the rest are destined to extinction.
I personally see the advancement of AI that lean on LLM's reaching a place of diminishing returns. I am not of the camp that AGI is around the corner nor do I believe that LLMs are capable of achieving all arenas of intelligence required to make AI truly revolutionary as many science-fiction enthusiasts would expect. And, if there has ever been a constant in humanity it is this: every technical revolution has added deep layers of complexity to our society's functions requiring more and more labor and experts to maintain the machine.
As it was aptly stated in the comedy The God's Must be Crazy:
The more man improved his surroundings to make life easier, the more complicated he made it. And civilized man, who refused to adapt to his surroundings, now finds he has to adapt and re-adapt every hour of the day to his self-created environment.
DOOM Fire Graphics
I found this great read on implementing the DOOM fire graphics using a basic array of colors. Its a nice breakdown by FABIEN SANGLARD who is another programmer: https://fabiensanglard.net/doom_fire_psx/
I've done a full implementation breakdown in C++ and SDL in a YouTube video.
vCard - Phone Contact Card VCF Format
The other day I had to get a listing of contacts from my phone and was able to get it exported as a VCF file through the iOS share options. I needed it as raw text so into the editor it went. This is the format of the VCF Contact List:
BEGIN:VCARD
VERSION:3.0
PRODID:-//Apple Inc.//iPhone OS 16.6.1//EN
N:Doe;John;;;
FN:John Doe
ORG:Landscaping;
TEL;type=CELL;type=VOICE;type=pref:(555) 555-5555
item1.ADR;type=HOME;type=pref:;;123 Fake St.;Dallas;TX;75000;United States
item1.X-ABADR:us
ADR;type=HOME:;;123 Fake St.;Dallas;TX;75000;United States
END:VCARD
BEGIN:VCARD
...
END:VCARD
BEGIN:VCARD
...
END:VCARDThankfully this format was relatively simple and I brewed up a basic php script to extract a set of contacts under the same ORG.
<?php
// get file contents from a file name passed in as an argument
$file = $argv[1] ?? null;
$contents = file_get_contents($file);
// using multi-line regex group VCARDs as text blocks in an array and loop them
if (preg_match_all('/BEGIN:VCARD.*?END:VCARD/s', $contents, $matches)) {
foreach ($matches[0] as $match) {
// filtering goes here, this example removes any VCARD that
// didnt have "FOORBAR ORG" in its contents
if (preg_match('/FOOBAR ORG/i', $match)) {
print_r($match);
}
}
}I then piped the script output into an inverted ack-search which filtered the output to fields I wanted to see.
$ php vdfextract.php Contacts.vcf | ack -v '(PRODID|BEGIN|END|VERSION|;;;)'I made a Mod for Oblivion
I took a programming side quest and created a MOD for the Elder Scrolls IV: Oblivion. This involved a deep dive into the Bethesda Gaming Creation Kit and was a good introduction to game modding overall.
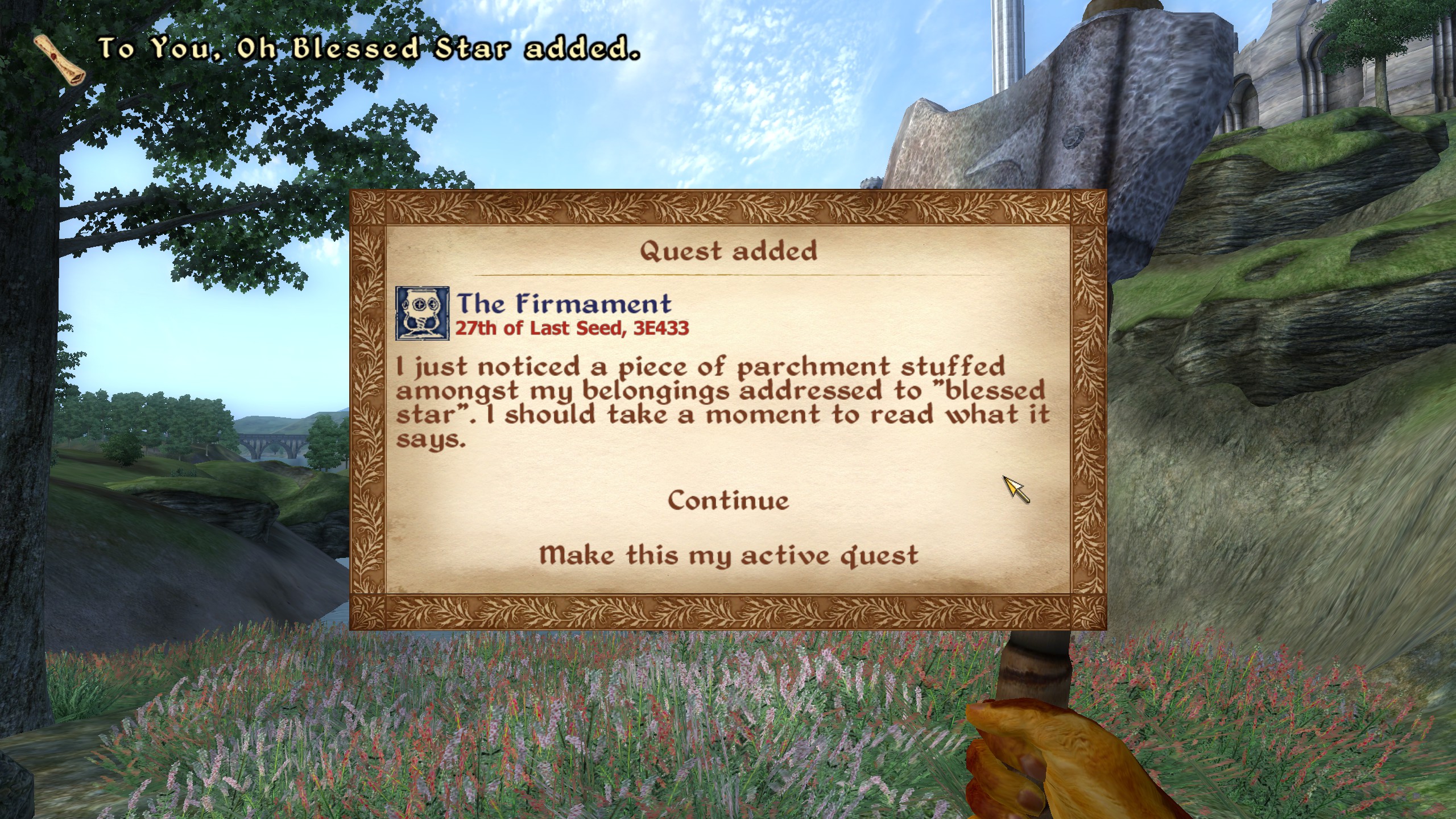
It was an exercise I did to experience the Bethesda Creation Kit tools of the early 2000s. In it I explored their purpose-built scripting language "Papyrus" and created a lore friendly mod for the community called "The Firmament."
Have you ever looked upon the stars of Tamriel and wondered at their wanderings? Have you ever scoured the constellations for your sign and to know if they are looking back at you? This mod is for you.
That's the catchline anyway.
I really enjoyed making this MOD and realized that it would pretty portable to Skyrim if I wanted.
The TES Construction Kit was really solid and well built and its no wonder such an incredible modding community has emerged around their titles. After the initial setup phase and trying to understand some conceptual elements, scripting and overall process, I was able to produce this Mod in about two days time.
One amazing quality of it is how the entirety of the Mod essentially sits on top of the core game, and you can overwrite any property of the game with a Mod, like pushing content onto a stack. This makes modifying everything in the game simpler and allows for fixing a variety of issues that plagued the original release.
Anyways, if you have a copy of Oblivion installed, head on over to the Nexus Mod link below and add The Firmament to your playthrough!
Play Online Game - Destroy Neo-Corporate Mass
Fly through space and shoot cool geometric objects in this (Desktop) space shooter sim! I built it with Three.js
All 3D rendering is done with Three.js, camera controls ported from other projects. Art by yours truly.
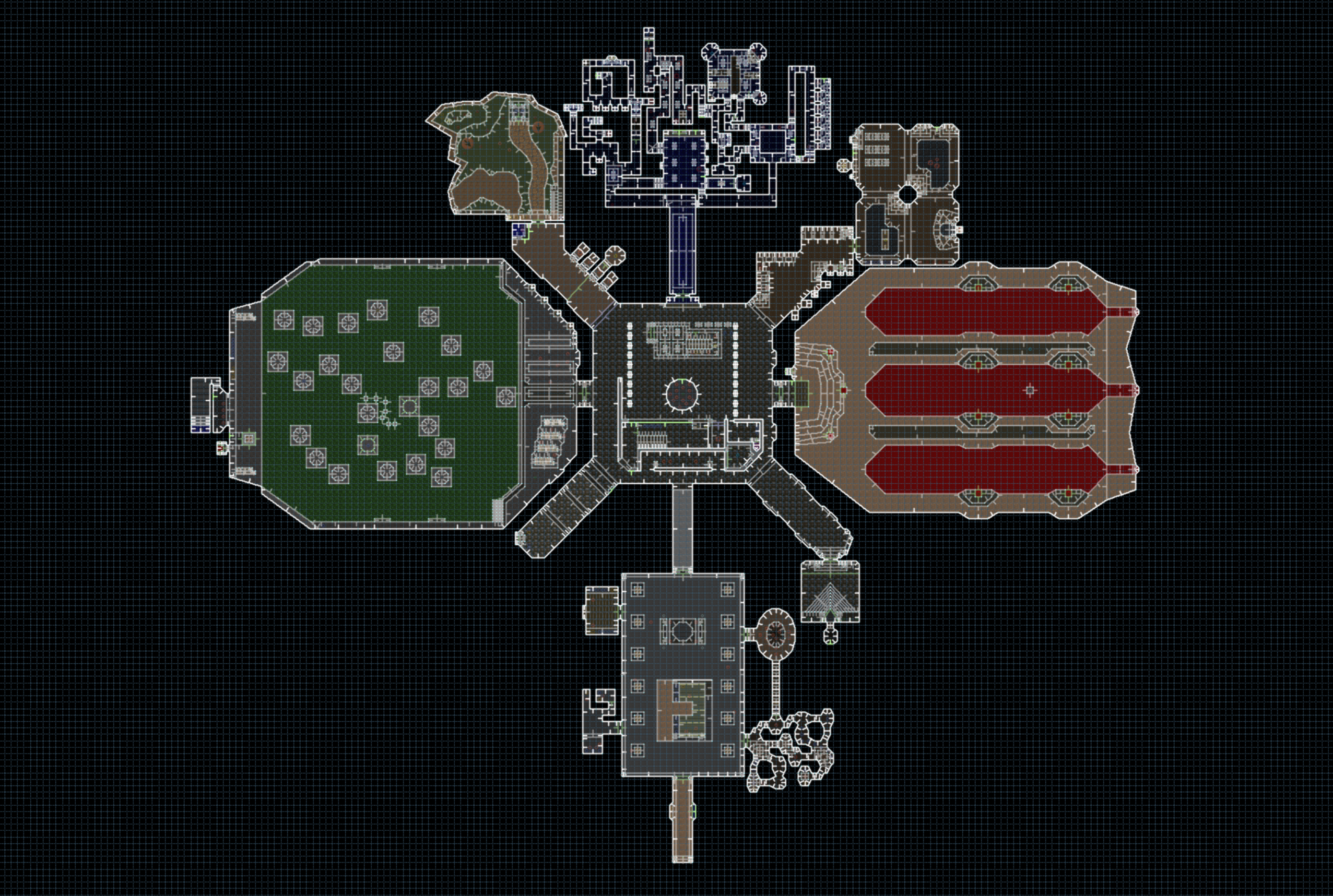
DOOM Level Development Guide - From WADs to Playing
I have written a deep dive into the DOOM level structure from binary formats of the WAD files to making a comprehensive and playable DOOM II level. This is an area that was overdue for a writeup so explore those pages as you can!
Reflections on Trusting Trust by Ken Thomson, 1984
Ken Thomson is a bit of a legend. Here is an eloquent and simple paper he wrote summarizing his 1983 Turing Award lecture titled "Reflections on Trusting Trust".
In the paper he demonstrates infecting the C compiler with a Trojan Horse that unwrites itself from the source code of the compiler while remaining in the binary version. This binary compiler then can infect any C compiled source code with a Trojan Horse of its own, all while leaving any original source code completely clean.
The moral of the story being: If you didn't write it, you can't trust it.
Is this sane to do in the modern world of software engineering? No. But its an interesting reflection in a world where millions of eyes comb open source code for vulnerabilities, which gives us an incredible defense against attacks (see the recent PHP ZLIB exploit attempt that was caught on GitHub), but it also gives us a false sense of security about what is actually running on our machines, servers and remote controls.
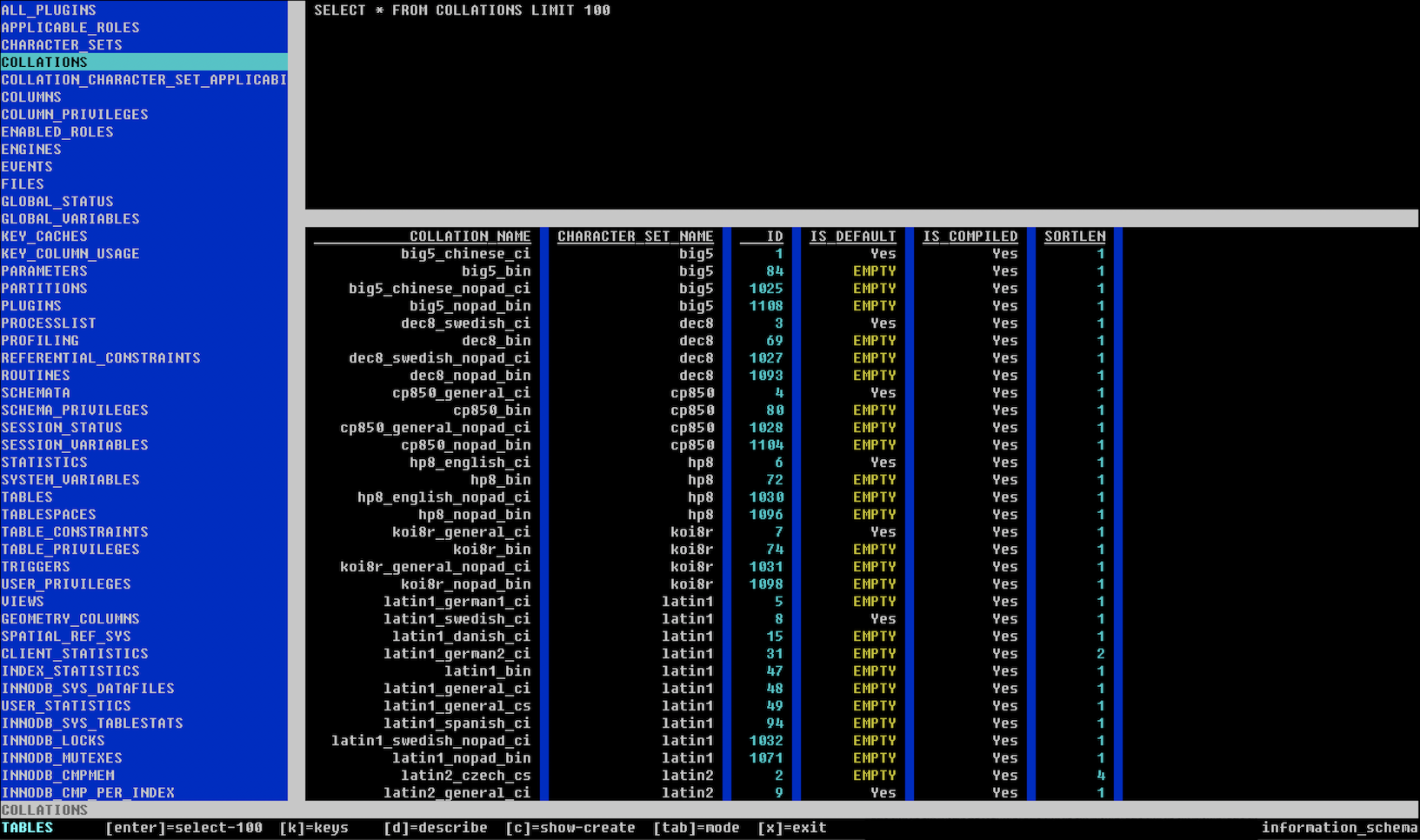
Introducing NCMySQL, an ncurses explorer and client for MySQL databases written in C
With the death of many great MySQL GUI clients such as SequelPro and the bloat of others I needed a replacement visual client for MySQL connections. I felt like it would be a great way to harness the experience working with ncurses and C to utilize the MySQL C API Library and create a basic TUI for working with it.
This project is completely open source and I encourage others with interest and experience to lend a hand.
New Video is Up! Bubblesorting in ADA
I have always been interested in the idea of ADA but never put my hands to it. I fell in love with strongly-typed languages after spending years in web development with loosely type langauges. So I wanted to explore ADA to see how extreme typing played out and how cumbersome or powerful it was. My small code was only to reproduce a BubbleSort on an Integer list, and I hope to do more with ADA soon.
Ada Programming - Implementing a Bubble Sort with Arrays and Procedures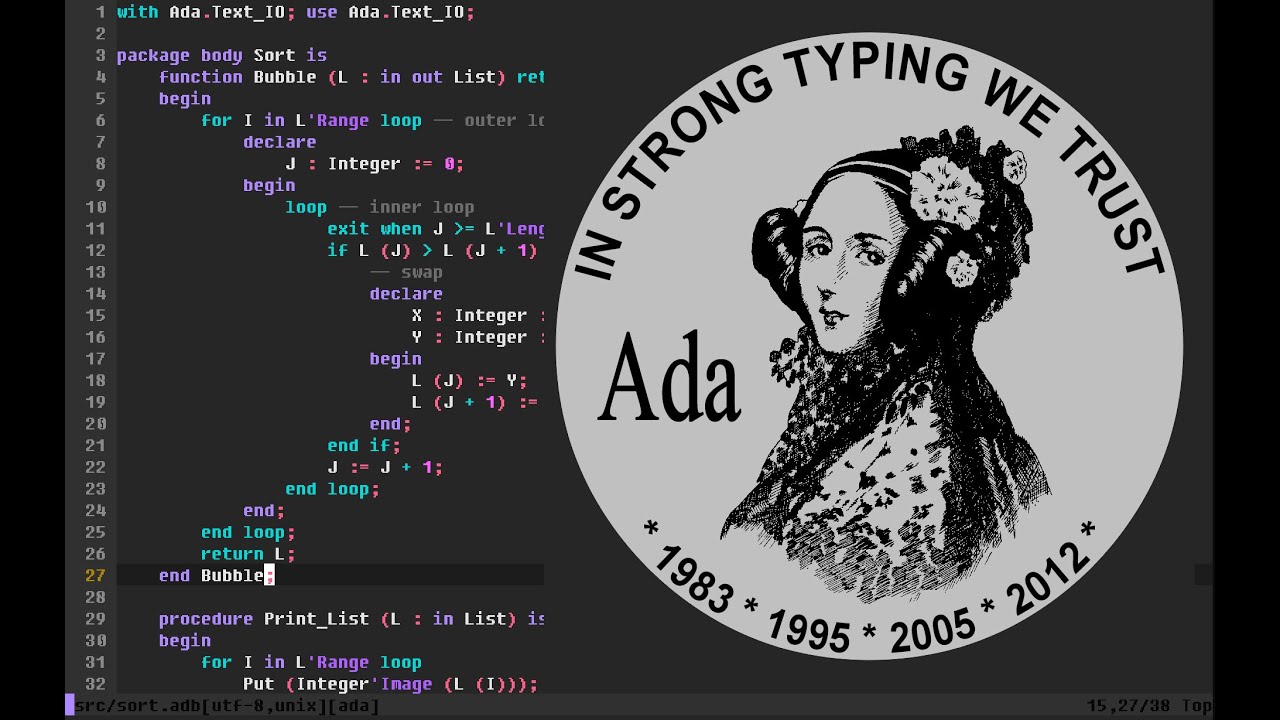
with Ada.Text_IO; use Ada.Text_IO;
procedure Bubble_Sort is
type Index is range 1 .. 5; -- lower bound can be anything
type Int_Array is array (Index) of Integer;
type Int_Array2 is array (Natural range <>) of Integer;
Arr : Int_Array := (1, 6, 4, 6, 8);
Arr2 : Int_Array2 := (7, 1, 4, 5, 6, 1, 2, 1);
begin
Put_Line ("Sort it");
for I in Index loop
Put (Integer'Image (Arr (I)));
end loop;
New_Line;
for I in Arr2'Range loop
Put (Integer'Image (Arr2 (I)));
end loop;
end Bubble_Sort;Python Doom Engine
This is a work in progress 3D reimplementation and exploration of the original DOOM engine. I am using Python as the main language. I explore 2D to 3D visualization techniques, raycasting, WAD file formats and 3D rendering engines.
Closures in C with GCC and Nested Functions
While doing some game developmeng on a C project I wanted to incorporate lambda functions into algorithm processing. You can see in several of my algorithm examples that I enjoy the use of functional programming to significantly reduce the complexity or performance issues that arrive out of processing the result of data using heap-allocated memory.
Combining GCC's extension support for nested functions and function pointers we can recreate the concept of a closure in C given that we have an environment that supports Executable Stacks!
Closures in C? Nested Function pointers with GCC, execstack and GDB debugging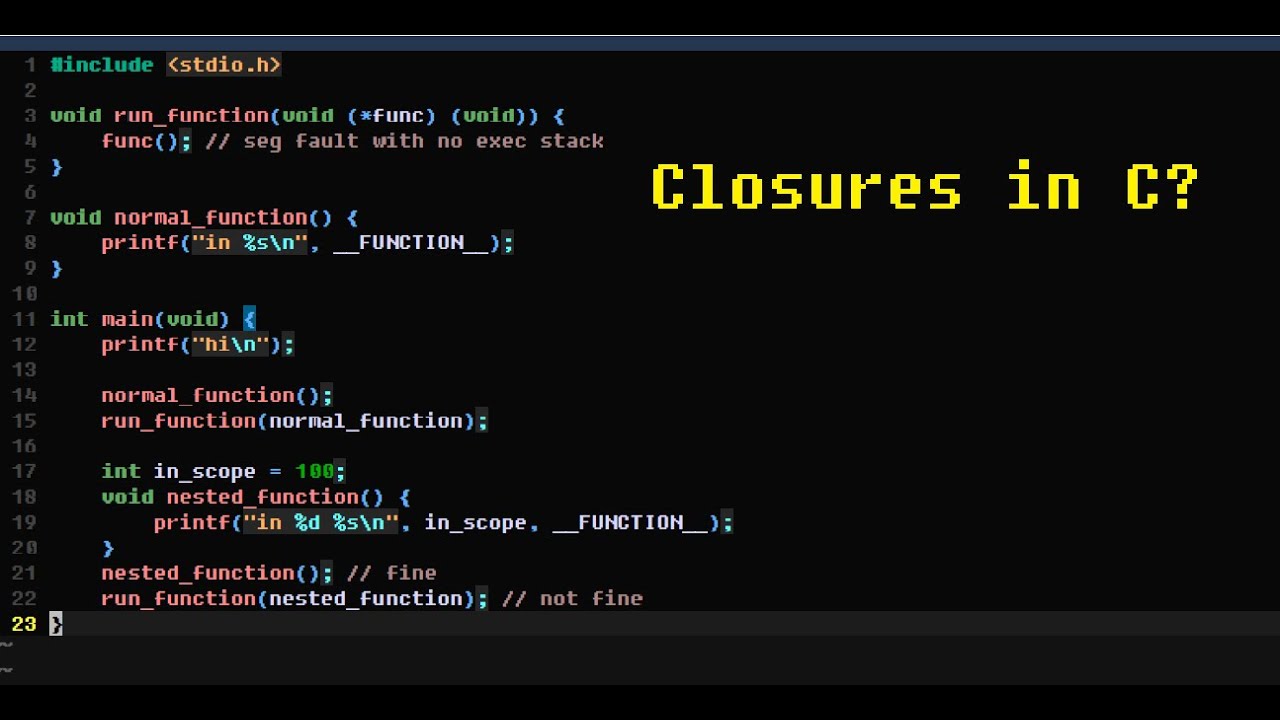
Elevator Simulator in Go
A Multi-threaded elevator simulator written in Go. Each elevator, person and floor operate as their own threaded state machines. Elevators, even when brought down to a simulated program, have a decently complicated set of states and rules for operating. When attempting to task an elevator for the most efficient routing it is not a simple challenge.
I utilized the RPC protocol to allow for the simulation to run in separated from a client. Clients could add passengers to the simulation and display it as either CLI text or a 2D graphics viewport. Below is the 2D rendering using Open GL.
Below is the text rendering of the elevator statuses.